- Main
- Computers - Networking
- The Rootkit Arsenal: Escape and Evasion...

The Rootkit Arsenal: Escape and Evasion in the Dark Corners of the System
Bill Blunden你有多喜欢这本书?
下载文件的质量如何?
下载该书,以评价其质量
下载文件的质量如何?
While forensic analysis has proven to be a valuable investigative tool in the field of computer security, utilizing anti-forensic technology makes it possible to maintain a covert operational foothold for extended periods, even in a high-security environment. Adopting an approach that favors full disclosure, the updated Second Edition of The Rootkit Arsenal presents the most accessible, timely, and complete coverage of forensic countermeasures. This book covers more topics, in greater depth, than any other currently available. In doing so the author forges through the murky back alleys of the Internet, shedding light on material that has traditionally been poorly documented, partially documented, or intentionally undocumented. The range of topics presented includes how to: -Evade post-mortem analysis -Frustrate attempts to reverse engineer your command & control modules -Defeat live incident response -Undermine the process of memory analysis -Modify subsystem internals to feed misinformation to the outside -Entrench your code in fortified regions of execution -Design and implement covert channels -Unearth new avenues of attack
年:
2012
出版:
2
出版社:
Jones & Bartlett Learning
语言:
english
页:
784
ISBN 10:
144962636X
ISBN 13:
9781449626365
文件:
PDF, 106.11 MB
您的标签:
IPFS:
CID , CID Blake2b
english, 2012
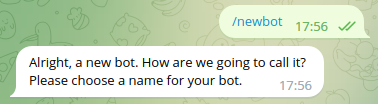
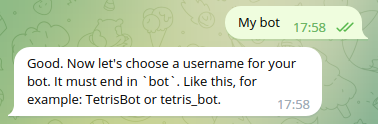
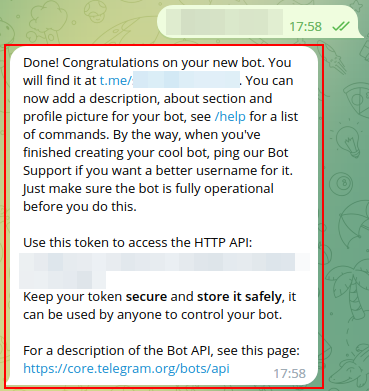
在1-5分钟内,文件将被发送到您的电子邮件。
该文件将通过电报信使发送给您。 您最多可能需要 1-5 分钟才能收到它。
注意:确保您已将您的帐户链接到 Z-Library Telegram 机器人。
该文件将发送到您的 Kindle 帐户。 您最多可能需要 1-5 分钟才能收到它。
请注意:您需要验证要发送到Kindle的每本书。检查您的邮箱中是否有来自亚马逊Kindle的验证电子邮件。
正在转换
转换为 失败
关键词
关联书单










































































 Amazon
Amazon  Barnes & Noble
Barnes & Noble  Bookshop.org
Bookshop.org  转换文件
转换文件 更多搜索结果
更多搜索结果 其他特权
其他特权